Yes it's fairy simple, basically you draw random things and think about what you want to write about, then the person who needs to read it just go back in time and reads your mind from that period using your paper card. People do it all the time, it's called Art. Go to museum and you find plenty of those.
No Stupid Questions
No such thing. Ask away!
!nostupidquestions is a community dedicated to being helpful and answering each others' questions on various topics.
The rules for posting and commenting, besides the rules defined here for lemmy.world, are as follows:
Rules (interactive)
Rule 1- All posts must be legitimate questions. All post titles must include a question.
All posts must be legitimate questions, and all post titles must include a question. Questions that are joke or trolling questions, memes, song lyrics as title, etc. are not allowed here. See Rule 6 for all exceptions.
Rule 2- Your question subject cannot be illegal or NSFW material.
Your question subject cannot be illegal or NSFW material. You will be warned first, banned second.
Rule 3- Do not seek mental, medical and professional help here.
Do not seek mental, medical and professional help here. Breaking this rule will not get you or your post removed, but it will put you at risk, and possibly in danger.
Rule 4- No self promotion or upvote-farming of any kind.
That's it.
Rule 5- No baiting or sealioning or promoting an agenda.
Questions which, instead of being of an innocuous nature, are specifically intended (based on reports and in the opinion of our crack moderation team) to bait users into ideological wars on charged political topics will be removed and the authors warned - or banned - depending on severity.
Rule 6- Regarding META posts and joke questions.
Provided it is about the community itself, you may post non-question posts using the [META] tag on your post title.
On fridays, you are allowed to post meme and troll questions, on the condition that it's in text format only, and conforms with our other rules. These posts MUST include the [NSQ Friday] tag in their title.
If you post a serious question on friday and are looking only for legitimate answers, then please include the [Serious] tag on your post. Irrelevant replies will then be removed by moderators.
Rule 7- You can't intentionally annoy, mock, or harass other members.
If you intentionally annoy, mock, harass, or discriminate against any individual member, you will be removed.
Likewise, if you are a member, sympathiser or a resemblant of a movement that is known to largely hate, mock, discriminate against, and/or want to take lives of a group of people, and you were provably vocal about your hate, then you will be banned on sight.
Rule 8- All comments should try to stay relevant to their parent content.
Rule 9- Reposts from other platforms are not allowed.
Let everyone have their own content.
Rule 10- Majority of bots aren't allowed to participate here.
Credits
Our breathtaking icon was bestowed upon us by @Cevilia!
The greatest banner of all time: by @TheOneWithTheHair!
I recommend the solitaire cipher.
From the Wikipedia article:
Solitaire leaks information at a rate of about 0.0005 bits per character. While its security may perhaps be adequate for very short messages, in general Solitaire is considered insecure.
Thanks for that! The analysis you present doesn't seem to account for the Jokers having variable values based on information only you and the receiver have predetermined, which is what I would propose to help solitaire be more secure. Also, a non-standard deck would help, such as a tarot deck.
It’s a good algorithm but if you need to decode any message, you must get drunk and listen to creepy radio stations at 1AM in the forest or something.
Hmm yea cool, problem is, its not reusable. You have to generate new keys every time. Kinda not easy to constantly exchange new keys if you are... say a group of revolutionaries hiding from the government. 👀
This is how all modern cryptography works. A deterministic cipher is functionally no different from pig Latin when it comes to actual security. An electronic solution like public key cryptography is infinitely more secure. If you're especially paranoid you can generate the cryptotext locally and send it by email; that would be much safer than anything you could achieve by hand.
I would think mailing a flash drive with the key and sending the message electronically would be safer. One requires knowledge of the other.
That's assuming the key and message are entirely independent. If you or the recipient isthe type of person or doing the types of things that would attract surveillance from a nation state (because realistically that's the one of the only scenarios where non-esoteric privacy practices might not cut it), it's not unrealistic that they'd intercept both your digital and physical mail and would be able to correlate them. At least with public key encryption, the private key is never actually in transit.
And that’s why if you’re in that position, you should have already shared your public key with them long in advance and your private key stays encrypted on an air-gapped laptop running Tails + CoreBoot. The message stays encrypted and you’re the only one with the physical device and knowledge to decipher it.
But that all comes down to security vs convenience. I’m super glad passkeys are starting to become available in a lot more places. They’re super convenient and if you use a password manager responsibly with a hardware key, they’re just as secure as the locks on your house.
Which is to say, not very, because ultimately nothing beats a $5 wrench.
That's why you make a stack of them. Generate hundreds up-front and you don't need to generate new every time.
Hmm okay I was actually thinking of using this for journaling... so keeping a stack of OTP codes right next to my journal isn't quite useful...
gotta keep my evil plans for world domination a secret... MUAHAHAHAHA 😈
Hmm, you're probably going to get a lot of answers assuming you wanted to do secure communication, not secure journaling. Different beasts I would think.
In-band periodic key-exchange. Pre-arrange that keys expire every X messages, and that the last (Xth) message is dedicated to sending the new key encrypted by the previous one.
I'm certainly not an expert.
But could you generate pads from mutually accessible data sources?
Like use hit_me_baby_one_more_time_not_a_virus.mp3 appended with a password, as a seed in a pseudo random number generating algorithm, then do the same thing with another data source, repeat however many times, then XOR the generated numbers together, and use the result as a pad?
That's no longer a one time pad. That's closer to a homebrew stream cipher with the weakness of having a key that you just hope no one notices.
Neat, yeah Wikipedia says steam cipher approximate one time pads but can also be completely insecure.
I think it would take one hell of an effort to crack, it would be like 3MB encryption right? Or if they guessed the scheme they could try all mp3s ever torrented XOR'ed in every possible combination.
Idk I think there's something workable there but I only having a casual knowledge
Also I think OP wanted pen and paper so maybe use a book instead digital files.
So, the size of the key doesn't directly relate to the size of the cipher, which also doesn't directly relate to security. AES is 128 bit , can have 128, 192, or 256 but keys and is currently not known to have any workable weaknesses.
Largely a cipher isn't weak if guessing the key is the only weakness, since every cipher is vulnerable to brute force. It's weak if you can figure out the message without needing the key.
So how does generating a one time pad from mutually accessible data fit into this scheme. Is the pad the cipher or the key?
If two people agreed that the pad would be the output of a particular pRNG given the 3rd paragraph of the second article on the third page of that day's newspaper as a seed.
The attack vector would be shortcomings in the pRNG I guess? Which could result in the possibility of some sort of statistical language attack?
Or the attacker could guess the newspaper text & algorithm.
If you want to calculate the cipher on paper everything that works on binary will be a huge overhead and basically require you to write stuff down for the calculations. So you need to burn sheets of paper for every en/decryption. So no XOR or anything.
I would go for a stream-caesar-cipher. Find a mathematical formula that you can calculate in your head and that gives you a numbers between 1-35 (or something similar depending on how many different characters you need). The formula must be pseudo random so f(x)=5, f(x+1)=1, f(x+2)=28, ... and not loop for a looooong time. Calculate a new value FOR EVERY LETTER OF YOUR TEXT!!!!! and use that as your Caesar cipher for that letter only (x is the position of the character in the text)
You need to keep track which letter in your cipher text was encoded with which x (write the x of the first letter of each page down) and keep the formula a secret. Never ever under any circumstance reuse an x. So you need to keep x going for every page/message and can't restart at 1 each time.
If x becomes to large and the calculations to complicated, its better to change the formula than to restart x. Never ever ever ever reuse the same cipher because then you get all the drawbacks of Caesar ciphers (probability of letters, length of words (position of the space character) etc).
Book cypher. 2 copies of the exact same book. The cypher is an agreed upon system of indicating letters or words.
No, not possible.
The closet we've seen are the zodiac killer's scribbles and they lasted as long as they did because he made a mistake (and frankly because no security researcher was really trying).
Modern cryptography works because it shuffles data around so much that it appears random. There's simply no way to do those sorts of operations with just pen and paper.
The chair is against the wall and John has a long moustache.
It's 11:59 on Radio Free America; this is Uncle Sam, with music, and the truth until dawn.
I was wondering if someone might recognize that
<< Et maintenant, les messages personelles. >>
You can do RC4 on pen and paper, more precisely 256 pieces of paper. There's also a variant of this cipher that uses deck of cards instead, RC4-52. There's also another stream cipher that uses deck of cards to store state and it's called Pontifex/Solitaire. Both have some weaknesses
VIC has way too short key for modern uses, but maybe there's a way to strenghten it
On related note, i guess that it would be possible to implement modern stream cipher with NLFSR in electromechanical machine, no silicon needed. WW2 era cryptography like this (enigma, M209 etc) were in a way stream ciphers and these require some of least hardware. Key storage and scheduling becomes bigger problem
Have a list of pregenerated numbers that each participant has, and do a ciphering system based on those. Like a book cipher, but smaller, more portable, and faster to eat in case of emergency.
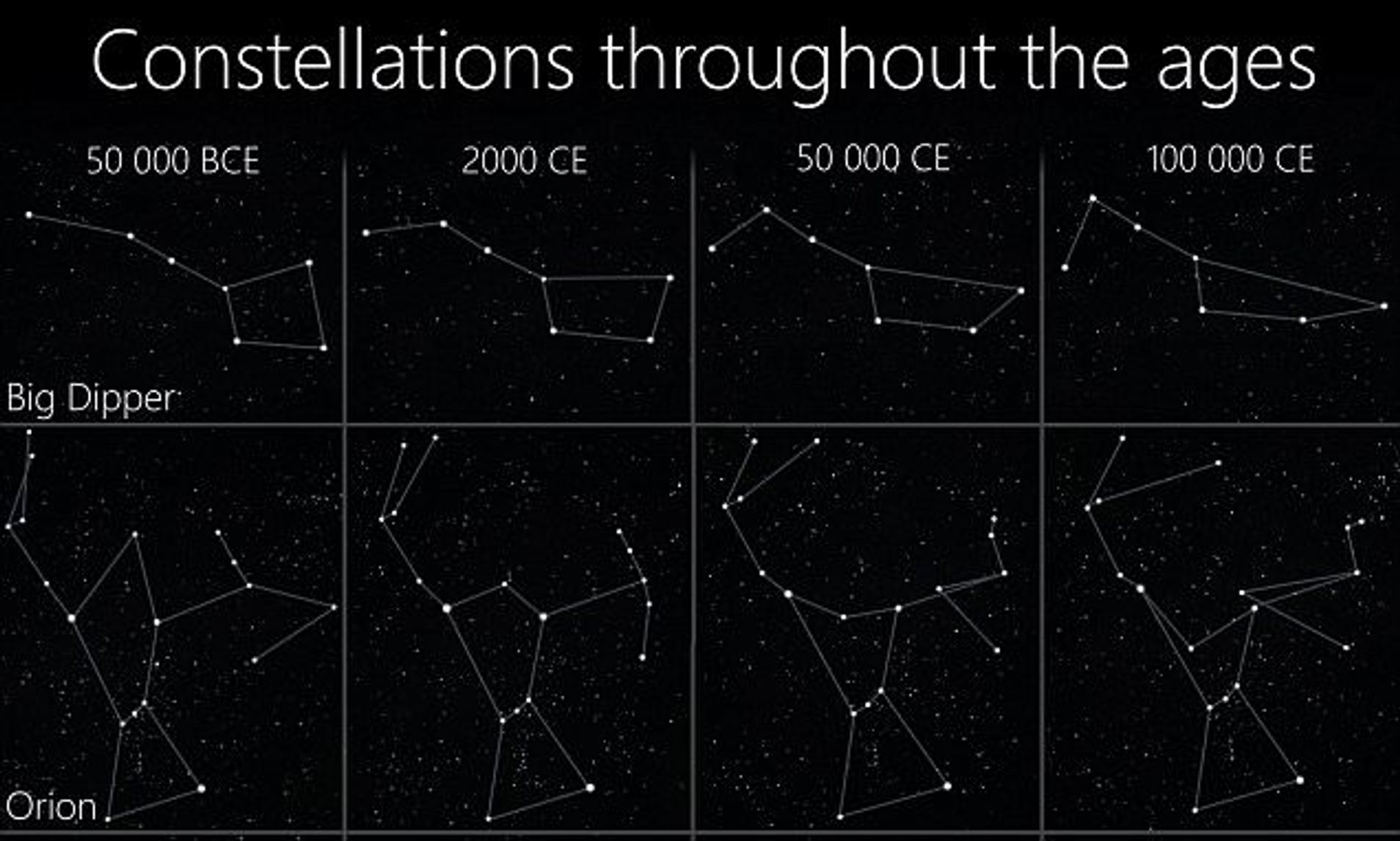
The code could associate skipped or unskipped symbols with the location of stars in the sky at a distant point in time unknown to those trying to break the code
You need a way to generate a psuedo random sequence that's synchronized. You can then use that random stream as something that works like a stream cipher.
Getting synchronized sources of random numbers like that isn't trivial, but it can be done.
To spitball a notion: get something like a small microcontroller that can drive a small screen, no wireless capabilities needed. Putting an implementation of something like the hotp algorithm on it will let you get some random data with each button press. That data can basically be used like a one time pad where you press a button each time you need more data. People decrypting the data just need to start at the same point in the sequence.
There are so many issues with this that I haven't thought of, but it's the most reasonable approximation of a pen and paper algorithm that has modern security levels and can be done in a reasonable amount of time.
Basically, you're going to want to look into stream ciphers. Since those can be done without feeding the data into them, it's possible to have a more disconnected system.
It's worth noting that against a governmental adversary, you're far more likely to be revealed via poor application of a custom crypto system than by a targeted bypass of a commonplace one.
If you're under suspicion, a cop can grab the piece of paper you did your work on out of the trash if you forgot to burn it and no decryption is required. Being physically readable, the key material can be seized and it's lost. If they have a warrant they can put a camera in your house and just record your paper.
With a cellphone, the lowest level of scrutiny that can use a backdoor that we know of would be a sealed fisa court order. Anything less official would require more scrutiny, since the NSA isn't going to send a targeted payload to the phone of a generic malcontent/domestic subversive.
Widely used crypto systems address an extremely wide array of possible attacks, most of which aren't related to the cipher but instead to issues of key management and rotation. This can give you guarantees about message confidentiality being preserved backwards in time if the key is stolen,cand only new messages being readable, as an example. (Perfect forward secrecy)
What you're looking for can be made, but you need to strongly consider if it actually makes you more secure, or less. Probably less.
Make your own language
Theoretically, if you made a new language based on English symbols, is it still just a cipher?
The Navajo did pretty well in WWII
Time to put my Chinese language skills to work?
English + Mandarin (Pinyin) + Cantonese (Jyutping) = ???
Canto-Mandar-lish? 🤔
Actually it might work. You'd need to understand 3 languages to decipher it.
Does the NSA/FSB/CCP have tri-lingual speakers? 🤔
Maybe I should learn some Navajo to add more fun to the mix? 😁
Learn Navajo and ancient Babylonian. Write everything in a custom pidgin of Mandarin, Navajo, and ancient Babylonian.
Also maybe microdots would be more effective. Not exactly pen and paper, but still analog. Hard to crack a code you can't find.
Just use a simple keyword like "TESLA" as your cipher. Sure, they can crack it, but they'll probably be wasting time in Colorado for weeks before they get to the end of your journal.
Maybe something akin to a book code, although machine learning may be able to crack those by that time.
I am not a cryptographer so I have no idea really.