this post was submitted on 07 Apr 2024
575 points (97.8% liked)
Programmer Humor
19522 readers
237 users here now
Welcome to Programmer Humor!
This is a place where you can post jokes, memes, humor, etc. related to programming!
For sharing awful code theres also Programming Horror.
Rules
- Keep content in english
- No advertisements
- Posts must be related to programming or programmer topics
founded 1 year ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
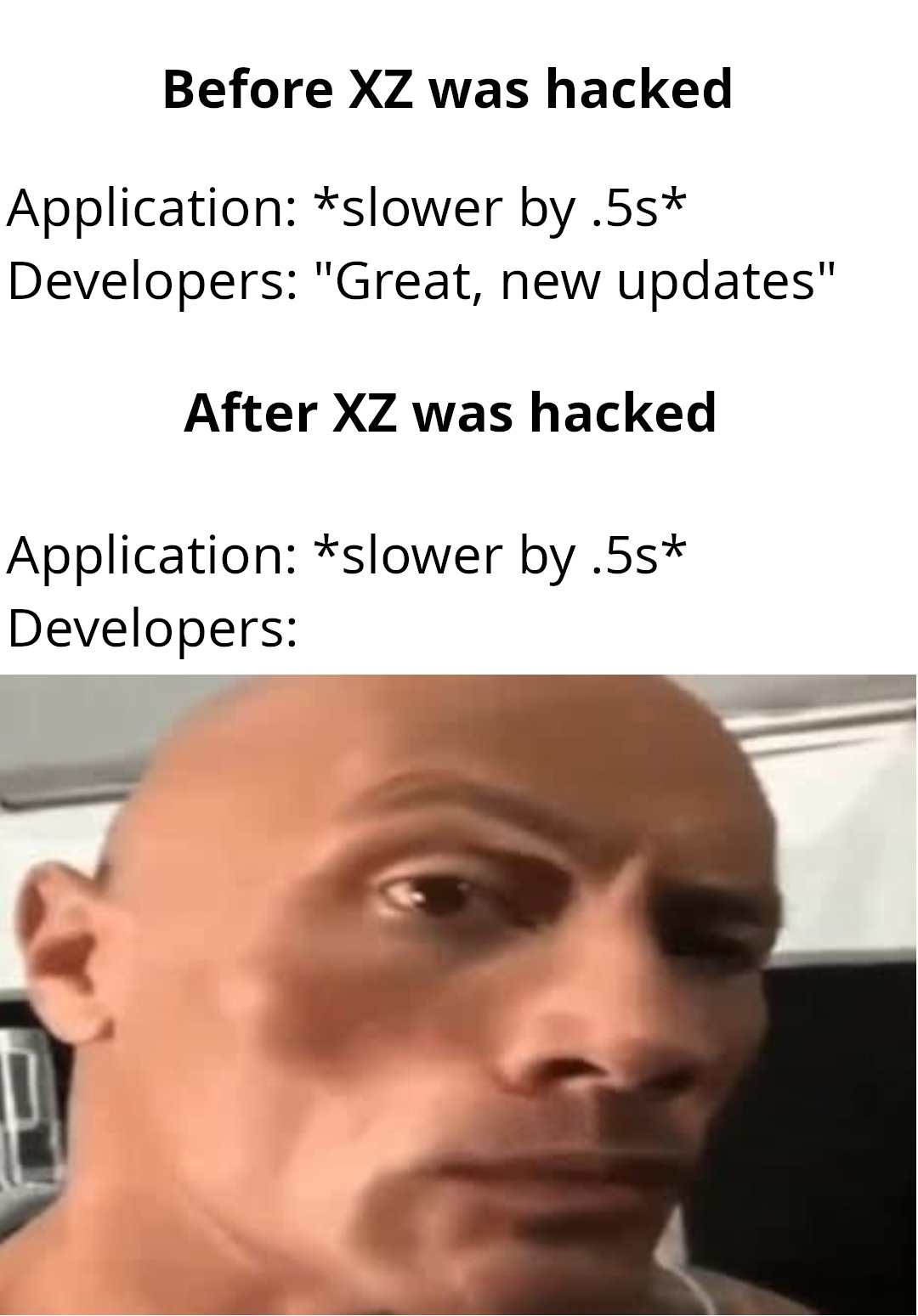
I think a lot of memes are missing the main point of how it was caught, the exploit caused a spike in CPU usage for a network call. That made no sense to the ~~guy~~ Messiah who found/reported it. FOSS software's strength is the number of critical eyes looking over each line of code you put out!
Right but the joke is that most developers aren't of that quality, and are now going to put leredditor super sleuth eyes on every application they build
What was the full story again? I'm googling but I can't find it.
In a nutshell, a backdoor was intentionally planted by a malicious actor in xz Utils, an open-source data compression utility widely used in Linux and other Unix-like operating systems. This discovery was made by Andres Freund, a developer and engineer working on Microsoft’s PostgreSQL offerings. He was troubleshooting performance problems on a Debian system. Specifically, SSH logins were consuming excessive CPU cycles and generating errors with Valgrind, a memory debugging tool. Through sheer luck and Freund’s careful eye, he eventually discovered that these issues were the result of updates made to xz Utils. Upon closer inspection, he found that updates to xz Utils were the result of a maliciously inserted backdoor. The backdoor, present in xz Utils versions 5.6.0 and 5.6.1, manipulated the sshd executable, allowing anyone with a predetermined encryption key to upload and execute arbitrary code on affected devices.
I expected a link to a source, but this is even better (matches with the little I remember)
Thanks!
No prob! I think Ars Technica had the best writeup imo: https://arstechnica.com/security/2024/04/what-we-know-about-the-xz-utils-backdoor-that-almost-infected-the-world/